Fortinet


Security-Driven Networking for a Hyperconnected World
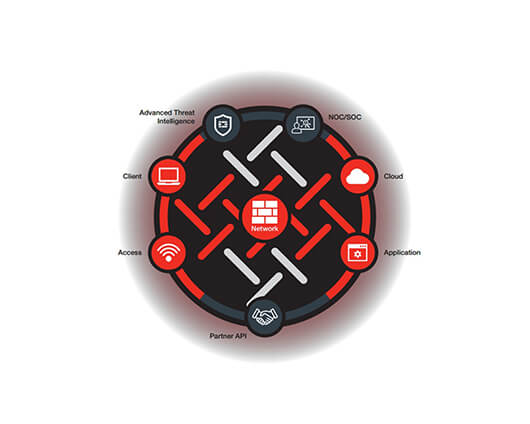
Fortinet offers a unified Security Fabric Framework to detect and adapt to the evolving threat landscape. After over 20 years, Fortinet has grown to become the number one in the most security appliances shipped worldwide. Trusted by more than 500,000 customers, Fortinet protects the largest enterprises, service providers, and government organizations around the world.
Fortinet Cybersecurity Solutions
Why choose Fortinet?
Fortinet leads the security market with its third generation network security to provide broad visibility and protection for the digital attack surface, integrated detection of advance threats, and automated response and continuous trust assessment.
Ready to Get Started?
Ready to
Get Started?
Connecting with MEC provides you with access to globally recognized technology brands and a range of premium value-added services.